The game is fully tested & guaranteed to work. It’s the cartridge / disc only unless otherwise specified.
Zen Intergalactic Ninja original NES Nintendo Game cartridge only – Cleaned Tested and Guaranteed to Work!
PRODUCT DETAILS
UPC:083717110347
Condition:Used
Genre:Action & Adventure
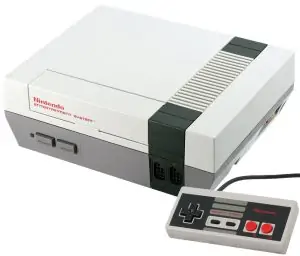
Platform:Nintendo NES
Region:NTSC (N. America)
ESRB:Everyone
SKU:NES_ZEN_INTERGALACTIC_NINJA
———This game is fully cleaned, tested & working. Includes the Disc/Cartridge Only. May have some minor scratches/scuffs.This description was last updated on October 28th, 2020.
We have a 121-day warranty period for all of our products. If you are experiencing any issues or aren’t satisfied with your item within 121 days, contact us and get your issue resolved. It’s that simple! View our full Return policy page here.
Every order is eligible for free shipping (5-7 business days) to any address in the United States. Orders to Canada are available for free shipping (9-12 business days) over $120! Expedited Shipping of 3-5 Business days is available in checkout. We ship worldwide! Shipping is via UPS, USPS or Fedex. We ship from Allentown, PA.












The Chief Information Security Officer has emerged as a key role in forward-thinking organizations that are keenly aware of the existential threat that cyber risks now pose. The authors of the CISO Desk Reference Guide grasp that reality and use their many years of experience to provide a ton of practical advice about how to function effectively in this role. The unique multi-author approach of the CISO Desk Reference Guide has produced a wealth of insight into the complex and challenging role of Chief Information Security Officer, a role that increasingly anchors organizational risk management in all things cyber and digital.From the excellent discussion of the evolving CISO role and how best to embed it in the organization, to fundamentals like data classification and controls, to advice on tools and techniques, the CISO Desk Reference Guide delivers multiple perspectives on the foundations of organizational cybersecurity. I would say this is essential reading for both aspiring and incumbent Chief Information Security Officers. The CISO Desk Reference Guide helps fill a critical gap in the ever-evolving information security common body of knowledge.
pretty good collection of CISO stuff. I read it for a client.
The content in this book is awesome. However the print quality could be a lot better. Especially the text insets such as the KEY POINTS or the ACTION ITEMS… the text is too small for comfort reading.Also, I wouldn’t mind paying more for a hard bound copy. These guys should make the quality of the book worth holding for a prospective CISO… instead it looks and feels like a low cost, me-too kind of a school book quality press, I feel.Please get a premium version out…
Just what I need for my first day on the job!!!!
The CISO Desk Reference Guide contains ‘real-world’ expertise on what a Chief Information Security Officer (CISO) needs to know and understand in order to be successful in his/her position within an organization. The authors have graciously attended panel discussions at the University in which I work, and provided students, faculty, staff, and community guests extensive information and guidance on how to secure their homes, businesses, and ensure their precious accounts remain safe from potential hackers.The CISO Desk Reference Guide is being reviewed for program integration, pulling details from this book (and their future CISO Refernce Guides as this is one of nine pending) into our cybersecurity program/courses. This book meets the academic requirements, and students and faculty appreciate its content, layout for comprehension, and verifiable discussions and recommendations (this it not fiction, definitely the real thing as it pertains to cybersecurity and the world of the CISO).Thank you – Bill Bonney, Gary Hayslip, and Matt Stamper for putting your minds and talents together to provide everyone with the true accounts of being a CISO…
My team and I here at Proven Recruiting have given this book as a gift to several our key clients. Many of them have commented that they are appreciative to have a resource such as this that provides insight and solutions to problems their organizations face every day. They can’t wait for volume two and neither can we.
This book is so crafted so well and it’s addressed to any security new or seasoned security executive. It demonstrates three different opinions on how to go about solving specific problems. It highlights that an information security program can’t be the voice/mind of a single person but that it takes a community. I highly recommend both volumes and I keep mine next to my desk at work as I usually refer to some areas of the books whenever I need additional data or direction. All three authors have a very pragmatic way on how to address risks while enabling the business to continue moving forward. This is the essential ingredient for any security program to be successful.Please check it out, hope there will be future volumes!
Good read for any aspiring ciso or even yet current ciso/managers.
As the father of one of the authors, my bias should be obvious. Still, controlling for partiality as best I can, it is obvious that Bonney, Hayslip, and Stamper have written a most timely and relevant guide to recognizing, navigating, and mastering the huge, potentially fatal risks associated with cyber security. By combining their years of education, experience, and wisdom, they have produced an essential work for the Digital Age. Practical and well-written,The CISO Desk Reference Guide is chockfull of examples of real-world risks, prevention measures, and remedies. Every chief information security officer (and key other corporate and government officials) would do well to give the guide a thorough read, and to keep it handy.
In fact, this book should be read by anyone who wants to be a CISO, works for a CISO, or is an executive or board member who depends on a CISO to keep the organization’s information and cyber risks under control.Here’s what I specifically liked about the book:* It gives thoughtful and thorough coverage of the CISO’s areas of concern.* The organization is innovative, which captured my attention.* The use of questions to inform each chapter is also very likable.* With each author’s voice clearly indicated, it’s useful to see three different ways of addressing the questions.* It’s neat how the three author perspectives merge into a single collection of recommendations at the end of each chapter.* I really like the end of chapter summaries. I almost wish each one appeared at the beginning of the chapter rather than at the end!After careful review, and a discussion with one of the authors, I have three constructive criticisms:1. I kept looking for some commentary on what a CISO should do when their great plan is regularly undermined by the regular internal fight for resources; when do you accept a loss and keep going versus starting to polish your resume for the next job?2. The book doesn’t clearly answer this question: Is the CISO’s problem space primarily a technology or a managerial one?3. The next edition should include a new chapter on "CISO Management and Leadership Tools and Strategies". This wouldn’t be a debate about which is better (manager versus leader), but a.